What is Zarp
Zarp is a network attack tool centered around the exploitation of local networks. This does not include system exploitation, but rather abusing networking protocols and stacks to take over, infiltrate, and knock out. Sessions can be managed to quickly poison and sniff multiple systems at once, dumping sensitive information automatically or to the attacker directly. Various sniffers are included to automatically parse usernames and passwords from various protocols, as well as view HTTP traffic and more
Zarp Features
- Poisoners
- Denial of Service
- Sniffers
- Scanners
- Services
- Parameter
- Attacks
Installation and Usage
git clone git://github.com/hatRiot/zarp.git
pip install -r requirements.txt
You can then run:
sudo python zarp.py –update
It is also recommended that user’s have the following installed for access to specific modules:
- airmon-ng suite (for all your wireless cracking needs)
- tcpdump
- libmproxy (packaged with zarp)
- paramiko (SSH service)
- nfqueue-bindings (packet modifier)
The recommended installation process is to run:
bryan@debdev:~/tools/zarp$ sudo ./zarp.py --help
[!] Loaded 34 modules.
____ __ ____ ____
(__ ) / _\ ( _ \( _ '
/ _/ / \ ) / ) __/
(____)\_/\_/(__\_)(__) [Version: 0.1.5]
usage: zarp.py [-h] [-q FILTER] [--update] [--wap] [--ftp] [--http] [--smb]
[--ssh] [--telnet] [-w] [-s] [--service-scan]
optional arguments:
-h, --help show this help message and exit
-q FILTER Generic network sniff
--update Update Zarp
Services:
--wap Wireless access point
--ftp FTP server
--http HTTP Server
--smb SMB Service
--ssh SSH Server
--telnet Telnet server
Scanners:
-w Wireless AP Scan
-s Network scanner
--service-scan Service scanner
bryan@debdev:~/tools/zarp$
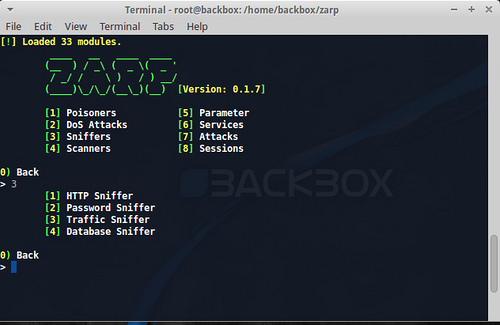
Main menu when launched with the command line GUI:
bryan@devbox:~/zarp$ sudo ./zarp.py
[!] Loaded 33 modules.
____ __ ____ ____
(__ ) / _\ ( _ \( _ '
/ _/ / \ ) / ) __/
(____)\_/\_/(__\_)(__)
[Version 0.1.4]
[1] Poisoners [5] Parameter
[2] DoS Attacks [6] Services
[3] Sniffers [7] Attacks
[4] Scanners [8] Sessions
0) Back
>
Navigating a module is pretty simple, and there are really only a few commands to know. When in the context of a module, the command 'info' can be used to dump a help or informational string:
ARP Spoof > info
---------------------------------------------------------
The heart and soul of zarp. This module exploits the ARP
protocol to redirect all traffic through the attacker's
chosen system.
http://en.wikipedia.org/wiki/ARP_poison
---------------------------------------------------------
+-----+------------------------------------+-------+------+----------+-
| | Option | Value | Type | Required |
+-----+------------------------------------+-------+------+----------+-
| [1] | Interval to send respoofed packets | 2 | int | False |
+-----+------------------------------------+-------+------+----------+-
| [2] | Address to spoof from target | None | ip | True |
+-----+------------------------------------+-------+------+----------+-
| [3] | Target to poison | None | ip | True |
+-----+------------------------------------+-------+------+----------+-
0) Back
ARP Spoof >
To set an option, give it the option number followed by the value:
ARP Spoof > 2 192.168.1.219
If an option supports a choice list, give it the option number followed by the lowercase letter o:
HTTP Sniffer > 2 o
[!] Options: ['Site Only', 'Request String', 'Request and Payload', 'Session IDs', 'Custom Regex']
+-----+-----------------------------+--------------+-------+----------+-
| | Option | Value | Type | Required |
+-----+-----------------------------+--------------+-------+----------+-
| [1] | Regex for level 5 verbosity | None | regex | False |
+-----+-----------------------------+--------------+-------+----------+-
| [2] | Output verbosity | 1 | int | False |
+-----+-----------------------------+--------------+-------+----------+-
| [3] | Address to sniff from | 192.168.1.97 | ip | False |
+-----+-----------------------------+--------------+-------+----------+-
0) Back
HTTP Sniffer >